3 Common Cyber Attacks That Target Businesses—and How to Stop Them
Introduction
For many business leaders, the world of cyber threats can feel like an impenetrable maze of technical jargon and ever-evolving tactics. Terms like malware, ransomware, phishing, trojans, SQL injection, and man-in-the-middle (MITM) attacks often blend together into one daunting list. It’s no wonder that even experienced professionals sometimes feel unsure about where to start.
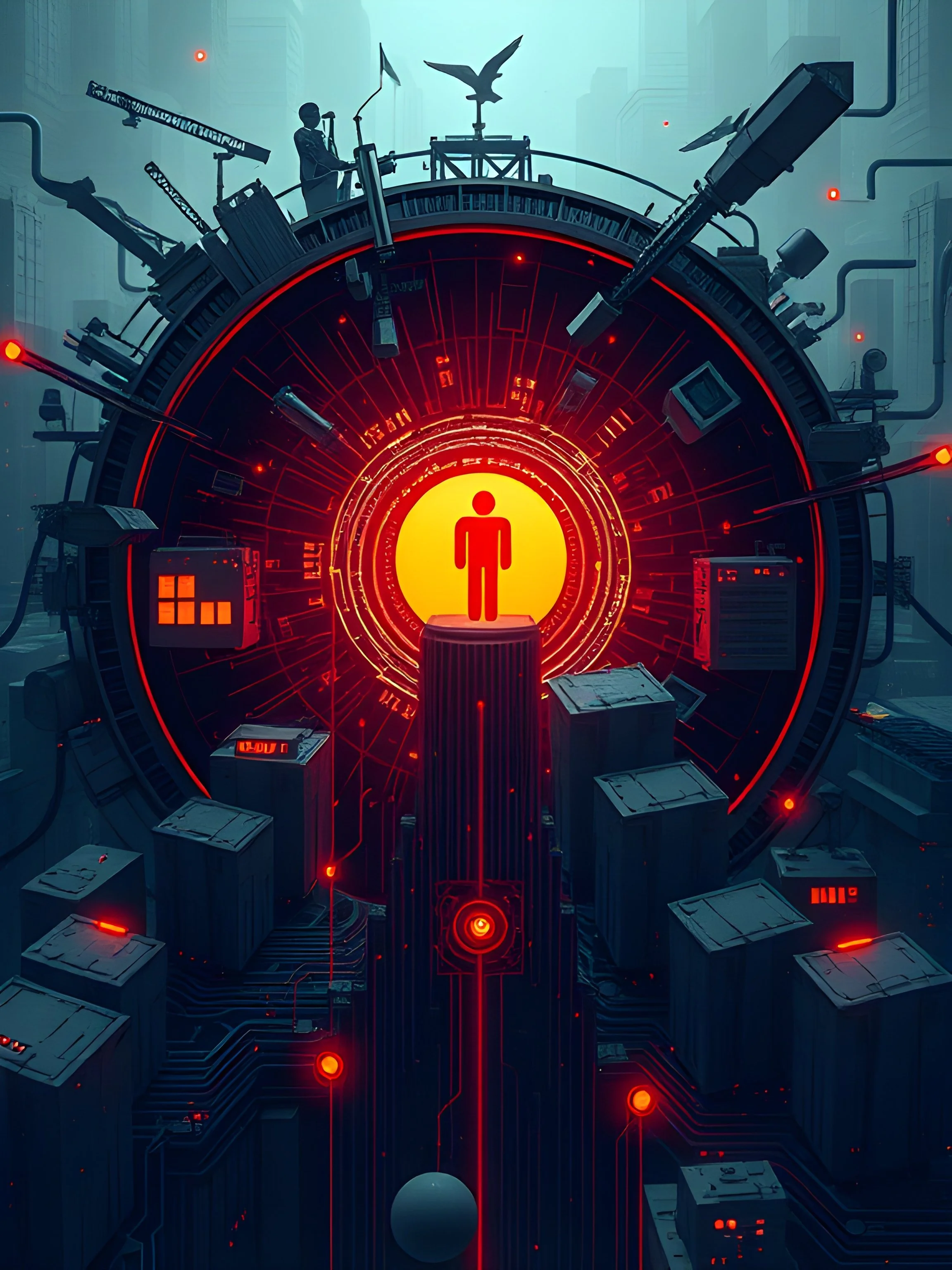
Yet, despite the complexity, a handful of threats stand out as particularly pervasive—and they frequently rely not just on technology, but on human behavior. In this blog, we’ll focus on three of the most prevalent threats you and your team are likely to face on a daily basis: phishing, malicious advertisements (malvertising), and browser permissions exploits. These threats are so dangerous precisely because they target the end user’s trust, attention, and habits.
By understanding how these attacks work and learning practical steps to identify and prevent them, you can better protect your organization’s data, reputation, and bottom line.
Cutting Through the Noise – Common Cyber Threats That Matter to You
The universe of cyber threats is vast, and it’s easy to feel overwhelmed by the sheer volume of new attack vectors. However, many of the daily risks facing businesses come down to a few key threats that exploit human nature as much as technical vulnerabilities. Instead of trying to master every term, let’s focus on understanding three common, user-focused threats:
Phishing: Attackers impersonate trusted sources—such as well-known companies, financial institutions, or business partners—to trick people into sharing sensitive data.
Malicious Advertisements (Malvertising): Seemingly legitimate ads can lead unsuspecting users to harmful sites or fake login pages, enabling criminals to harvest credentials or infect devices with malware.
Browser Permissions Exploits: Cybercriminals trick users into granting unnecessary permissions—like notifications, camera access, or location tracking—allowing them to bypass other security measures.
What sets these threats apart is their reliance on user action. Defending against them isn’t solely a matter of installing the latest security software; it also requires cultivating an informed, cautious, and security-minded workforce.
1. Phishing - The Art of Deception
Phishing remains one of the most dangerous and persistent cyber threats. According to numerous cybersecurity studies, it’s responsible for a significant portion of all reported security incidents. The reason? It targets people rather than systems, enticing well-intentioned employees to hand over the keys to the kingdom.
How Phishing Works
Phishing attacks often come in the form of emails, text messages, or phone calls, all designed to appear as if they’re coming from legitimate sources. These messages typically urge you to:
Click a link to “verify” your account.
Download an attachment that appears important.
Enter login or financial details on a page that looks genuine but isn’t.
Sophisticated attackers meticulously craft these messages to blend into a user’s daily routine. A request to reset an email password, approve a vendor invoice, or confirm payment details can appear completely legitimate.
Recognizing Phishing Attempts
To spot phishing attempts, stay alert to:
Sender Verification: Email addresses can be spoofed. Always confirm requests by contacting official channels.
Links and Redirects: Hover over links (on desktop) to check their true destination before clicking.
Unusual Requests: If it feels off—like an urgent request for sensitive data—it probably is.
Context Mismatches: Does the tone, timing, or content match what you’d expect from the sender?
Protecting Against Phishing
Employee Training: Regular awareness training helps employees recognize suspicious messages.
Robust Email Filtering: Use security tools to filter and flag high-risk messages before they reach inboxes.
Multi-Factor Authentication (MFA): Even if credentials are compromised, MFA adds another layer of defense.
Verification Procedures: Encourage employees to confirm unusual requests via a known phone number or direct conversation.
2. Malicious Advertisements - Hidden Traps in Plain Sight
Malicious advertisements (also known as malvertising) differ from phishing attacks in that they often appear in places we trust—like well-known websites or the top results in a search engine. They’re designed to blend seamlessly with legitimate content, increasing the likelihood that users will click without thinking twice.
How Malvertising Works
Malvertising generally unfolds in two ways:
Redirection to Malicious Sites: A user clicks on what appears to be a normal ad, only to land on a site designed to steal login credentials or distribute malware.
Drive-By Downloads: In some cases, simply loading the webpage containing the ad can trigger hidden scripts that download malware in the background, especially if the browser or operating system isn’t up-to-date.
Recognizing and Avoiding Malicious Ads
Malvertising’s strongest weapon is its disguise. Here’s how to spot and steer clear of these threats:
Search Engine Results: The first few links in a search often show the word “Ad” or “Sponsored” next to them. While many sponsored links are legitimate, be cautious. Consider scrolling down to the organic results or, better yet, navigating directly to the site by typing its URL into your browser.
Deceptive Website Ads: Ads within a webpage can look like part of the site—buttons, menus, or even login prompts. For example, you might click on what you believe is a headline for a news article only to be redirected to a suspicious sign-in page. If you re-enter your credentials and find yourself back at the homepage with no sign of the article, you may have just handed your login details to a criminal.
Consistency Checks: If something doesn’t feel right—like being asked to log in again unexpectedly—double-check the URL. Make sure you’re on the correct domain. Legitimate sites rarely ask for repeated logins in quick succession.
Mobile Browsing Challenges: On a phone or tablet, you can’t hover over a link before tapping. Be extra cautious with pop-ups or links that appear overly eager for you to click through. If in doubt, navigate directly to the main site and find the content through the site’s search or menu.
Protecting Your Business from Malvertising
Employee Awareness: Teach your team to be skeptical of ads that seem too convenient or appear to mimic site elements.
Ad and Script Blockers: Consider deploying browser-based ad blockers or script-blocking plugins.
Regular Updates: Keep browsers, plugins, and operating systems current. Many drive-by attacks exploit known vulnerabilities that patches can fix.
Limited Permissions: Restrict administrative privileges on employee devices. Reduced privileges can prevent the automatic installation of malware.
3. Browser Permissions Exploits - Granting the Wrong Access
Modern web browsers offer useful features—like notifications, microphone and camera access, or location services—to improve user experience. Unfortunately, cybercriminals exploit the trust we place in these prompts. By convincing users to grant unnecessary permissions, attackers can gain unprecedented access to sensitive data or systems.
How Browser Permissions Exploits Work
Common tactics include:
Malicious Extensions: These appear helpful but actually harvest credentials or inject malicious code.
Example: Threat actors often create malicious browser extensions that mimic legitimate ones, such as ad blockers, by copying their logos, names, and descriptions to appear authentic. For example, a fake ad blocker extension might promise to block intrusive ads but secretly track your internet activity, logging the websites you visit and even capturing sensitive data entered online. These malicious extensions often make their way onto browser stores with misleading positive reviews or inflated download counts to appear trustworthy.
Fake Prompts: Attackers display permission requests that seem routine, yet grant behind-the-scenes control over browsing behavior.
Example: Browser permission exploits often appear as routine requests, such as granting notification or location access. Once approved, attackers can track browsing behavior, send scam notifications, or redirect users to harmful sites. To stay safe, scrutinize all permission requests.
Clickjacking: Invisible elements trick users into clicking “Allow” even when they intend to click something else.
Recognizing Browser Permissions Exploits
Unexpected Prompts: If a site suddenly asks for camera, microphone, or even notifications permissions, pause. Is it necessary for the task at hand?
Frequent or Repetitive Requests: Legitimate sites rarely bombard you with permission prompts.
Out-of-Context Requests: A news site doesn’t need your microphone. A blog post doesn’t require your camera. Always ask: Is this permission reasonable?
Protecting Against Permissions Exploits
Permission Management: Configure browsers to prompt for permission every time, instead of granting blanket approval.
Extension Reviews: Regularly review and remove unused or suspicious browser extensions.
User Training: Make sure employees know to deny suspicious requests and report them to IT.
Practical Cybersecurity Tips for Businesses
Defending against these user-focused threats requires a layered, proactive strategy:
Train Employees: Regular, well-structured training sessions can dramatically reduce the risk of successful attacks.
Implement Layered Defenses: Combine email filtering, DNS filtering, endpoint protection, and other security tools for comprehensive coverage.
Enforce Secure Browsing Practices: Ad blockers, script blockers, and careful review of permissions help prevent accidental clicks.
Use Multi-Factor Authentication (MFA): Add another barrier to entry for sensitive accounts.
Develop a Response Plan: Have a clear, tested incident response process so you’re prepared if an attack occurs.
Seek Expert Guidance: Cybersecurity professionals can tailor solutions and recommend strategies that align with your business goals and risk profile.
Key Takeaways
Phishing: Train employees to verify and question unexpected messages, links, or attachments.
Malvertising: Recognize that even trusted sites can host deceptive ads—stay vigilant and rely on safe browsing tools.
Browser Permissions Exploits: Limit or scrutinize permissions, and keep a watchful eye on extensions and prompts.
Ongoing Effort: Cybersecurity isn’t a one-and-done task. Maintain continuous training, updates, and improvements.
Professional Help: Don’t hesitate to seek help from experts who can strengthen your cybersecurity posture.
Conclusion: A continuous Journey of Vigilance and Education
Cyber threats are evolving constantly, but many of the most damaging attacks still hinge on human decisions. By understanding the nature of phishing, malvertising, and browser permissions exploits, you empower your team to make smarter choices online. Combine this knowledge with technical safeguards, well-defined policies, and expert guidance, and you’ll create an environment where would-be attackers face significantly higher hurdles.
Remember: cybersecurity is not a destination—it’s a journey that requires ongoing attention and adaptation. Start today by raising awareness, refining your processes, and building a culture that values security. Over time, you’ll transform from feeling overwhelmed by cyber threats to confidently navigating the digital landscape.
If you need assistance or guidance in strengthening your organization’s defenses, don’t hesitate to reach out. Together, we can lay a stronger foundation for a safer digital future.
Protect Your Business Today
Call Us: 432-620-9457
Email: help@extsys.com
Cyber threats are evolving, but proactive steps can keep your business safe. Educate your team, strengthen your defenses, and prepare a response plan now. For expert guidance tailored to your needs, contact us and safeguard your organization’s future.